Prerequisites
Setup
Thecyber-dojo Kosli organisation is public, so any authenticated user can read its data:
Start with the environment
https://cyber-dojo.org runs in an AWS environment that reports to Kosli asaws-prod. Get a log of its recent changes:
creator:b7a5908 started in snapshot #176, and creator:31dee35 stopped in snapshot #177. The new artifact arrived just before the 500 error — that is the one to investigate.
Dig into the artifact
Get the full history ofcreator:b7a5908, using the fingerprint prefix from snapshot #176:
aws-prod at 16:51 — right when the incident began. The output includes a direct link to the git commit.
Follow to the commit
Open the commit URL from the output: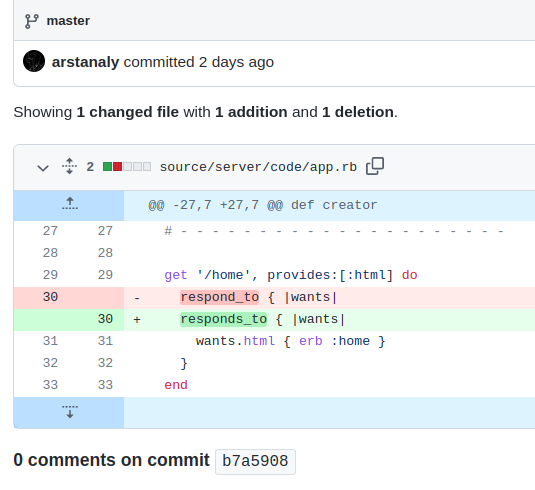
app.rb — an extra s inserted into the method name. The function is called respond_to, not responds_to. That one character caused the 500 error.
What you’ve accomplished
You traced a production 500 error back to a specific git commit — without any direct access toaws-prod. By querying the environment log and artifact history in Kosli, you identified exactly which deployment introduced the incident and which code change caused it.
From here you can:
- Learn more about environment and artifact queries in the Querying Kosli tutorial
- Learn how to follow any commit from CI into production with the From commit to production tutorial